Technology is fast becoming an integral part of businesses worldwide.
From emails and financial correspondence to CRM softwares and collaborative work documents. In a world striving to automate processes and give every employee the freedom of working remotely, we cannot overemphasize the importance of good security.
When telecoms giants, TalkTalk, had their personal data compromised in 2015, one of the highest-profile cyber attacks came in, resulting in a record fine of £ 400,000 for security failures. Similarly, Three Mobile was also the target of a cyberattack that revealed the information of more than 200,000 people.
It is not just the big business that has to worry about cyber attacks, I believe the small businesses have much more to lose; they are at their foundation stage and most are not aware of cybersecurity best practices.
Here are some of the more rampant cyber dangers and the easiest way to deal with them.
Data Leaks
One of the more popular threats to cybersecurity is data leaks, it can be extremely damaging to both businesses and individuals. All businesses generate and hold a range of data, from employee records to customer insights and financial documents, all these contain sensitive information that can easily put a business and its bottom line at risk.
One of the ways your business can ensure its data is protected from any leaks is by limiting the amount of information available to the public domain, but this is still no better than a stopgap measure. You are advised to onboard to reliable tools that automatically protect your data and close all access to confidential data to people both in and out of your business.
A prime example of a program that can help with this is Microsoft 365, with its tools that are fully integrated and security protocols that authenticate individual users and segment information by departments and individuals.
Related: Microsoft 365 and how it helps small businesses.
Ransomware
Ransomware, which is a type of malware that encrypts the data of a company and is only unlockable in return for a large fee, is another cybersecurity threat to companies. Although data stored on computers may be at risk from ransomware, with the proliferation of cloud services for storing data, these forms of cyber attacks have also increased in prominence.
The primary issue being that whilst most companies wish to onboard to the cloud, they do not know the parameters to look out for when picking out good cloud service providers, to find out more on cloud service providers and which ones suit your needs more click here or click here to book a consultation for free.
Malicious software may be constantly developing but security software adapts to eradicate threats even as they come up. That’s why it’s so important that your business keeps its antivirus software updated at all times.
We must bear in mind that not all antivirus can cope sufficiently with ransomware. Businesses need to ensure they adopt solutions that can properly protect against a cyber attack.
One of the best options on the market is Kaspersky which uses deep learning and adaptive protocols to anticipate and protect against the widest range of attacks and supports existing options with its seamless integration powers.
Phishing
In 1970, John Dapper created the infamous Blue Box used to hack telephone systems, known as phone freaking. As time passes, technology advances but so too have the methods by which phishing is conducted.
Phishing is said to be the process of fraudulently attempting to gain an individual’s information to exploit all accounts associated with the data, from email accounts to bank accounts.
Even as technology rises to put a stop to these acts, it also rises in favour of them. With the rise of artificial intelligence, these attacks can even be automated.
To ensure your business doesn’t fall a victim to a phishing scam, you are advised to onboard your trusted email service providers, these providers are capable of automatically detecting and weeding out scam mails also known as spam.
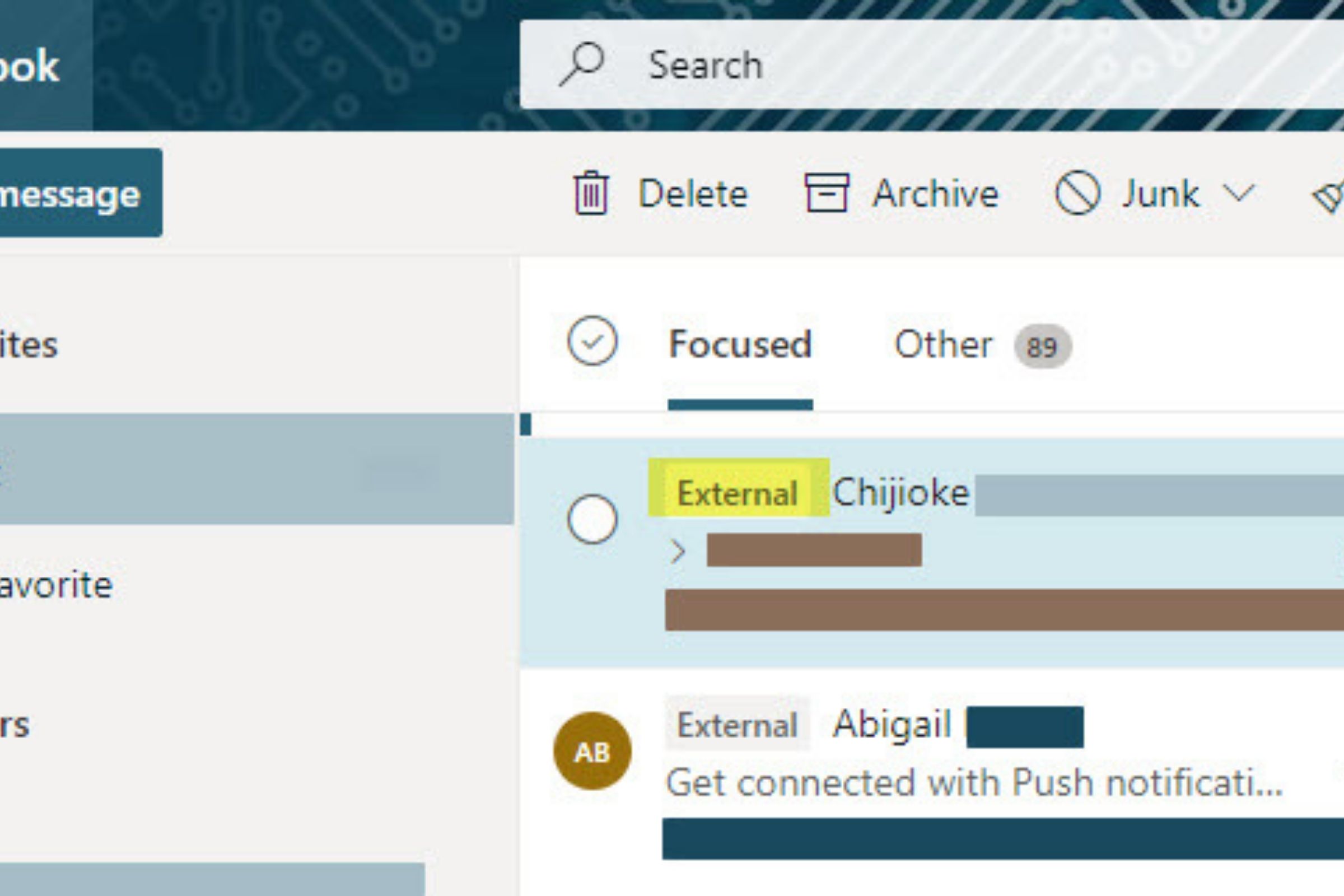
A perfect example of one of such providers is Microsoft Outlook, with intelligent security protocols that can monitor your activity, segment data and weed out annoying trackers, you are all but guaranteed safe travels in the waters of the internet.
Related: What is the difference between Microsoft Outlook and other email providers?